Companies in dozens of countries have been caught out by malware exploiting older, unpatched Windows machines.
Update: Organizations and individuals across the UK, Europe and beyond are scrambling to restore their computer systems after a ransomware program called WannaCry caused an unprecedented level of disruption over the weekend.
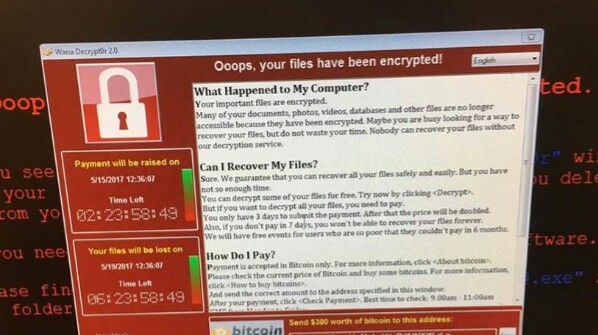
In the traditional ransomware style, WannaCry demands bitcoin payments before it will unlock files that have been encrypted on users’ machines, as well as spreading itself automatically to other networked computers. It’s believed that the malware exploits a security hole in unpatched, older versions of Windows, including Windows XP.
On Sunday, Europol said 200,000 victims in 150 countries were believed to be hit so far, with another wave of attacks potentially on the way as people begin to switch their office computers back on on Monday morning – giving the ransomware new ways to spread.
Stay on guard
The National Cyber Security Centre in the UK is warning both businesses and individuals to be on their guard, especially those running older versions of Windows. The NCSC site also includes some smart advice for protecting your computers against ransomware of this kind.
The NHS in the UK, Telefónica in Spain, Renault in France and dozens of other companies are believed to be affected, with reports that WannaCry has now spread to more than a hundred countries. Microsoft has taken the unusual step of pushing out a Windows XP security patch for the bug, some three years after official support for XP ended.
As of Sunday afternoom, the scale of the damage was still being assessed, and it’ll be some time yet before affected systems can be cleaned up and put back on their feet. It’s safe to say if you’re struggling to connect with any kind of computer system this weekend, anything from train times to doctor appointments, WannaCry could be to blame.
Header image via @fendlife.
The NHS in the UK was one of the first organizations to raise the alarm, and our original report continues below.
The NHS has confirmed that a number of hospitals across England have been the victims of a large scale cyberattack, with NHS employees taking to social media claiming that PCs in their hospitals were displaying a message saying “your computers are now under their control and pay a certain amount of money. And now everything is gone.”
Taking over a PC and threatening to delete its data unless money is paid is a classic move of ransomware viruses, and while they can cause anguish and disruption when infecting home and business machines, when it comes to hospitals lives could be at stake.
Affected hospitals are postponing all non-urgent activity and are asking people not to come to A&E. Instead people should dial 111 for urgent medical advice, or 999 if it is a life-threatening emergency.
A statement released by East and North Hertfordshire NHS trust, which covers some of the hospitals affected, says that “today (Friday, 12 May 2017), the trust has experienced a major IT problem, believed to be caused by a cyber attack.
“Immediately on discovery of the problem, the trust acted to protect its IT systems by shutting them down; it also meant that the trust’s telephone system is not able to accept incoming calls.”
According to the BBC, the attack has also spread across Europe, hitting mobile brand Telefonica too. It increasingly appears to be a sophisticated, coordinated attack.
Warning signs
Unfortunately, it was only a matter of time before a cyberattack of this scale would hit hospitals, with a warning from Andrew Avanessian, vice president at Avecto, a global security software company, circulating a few days ago that said that “hospitals are often targets due to the value of the data they hold. Not only does patient data have a resale value, it’s sensitive enough that NHS Trusts are likely to pay a ransom to get it back if it becomes encrypted.”
While we’d often advise people infected by ransomware to contact the police before paying any sort of ransom – mainly because there’s no guarantee that the malicious users behind the malware will release your data even if they get paid – the NHS doesn’t have that luxury considering lives could be at stake.
Avanessian suggested that it could be outdated software that caused the problem here, saying “outdated systems can often be to blame, and it’s bad news for patients that 90% of Trusts are running old versions of Windows that are riddled with security holes.”
He suggested NHS trusts update their software as soon as possible, but sadly it looks like it’s too late.
Road to recovery
“We commend NHS England on reacting so quickly, and for being open about this attack,” said Chris Ross, Senior Vice President, International at storage giants Barracuda.
“Healthcare records holding sensitive and personal data are 100 times more valuable than stolen credit card details, so it comes as no surprise to see that NHS England has been targeted in this way.
“Having been attacked the focus now must be to recover with minimal disruption. We would hope that the hospitals that have been hit have already devised and implemented a comprehensive backup recovery plan that will allow them to recover all encrypted files with minimal effort.
“This just goes to prove that cybercriminals don’t care who they target with ransomware, as long as the victim is willing to pay. All sizes of organisations have been targeted, and the impact is far reaching. It’s not just your hard-earned money that is at risk, it’s also your reputation, viability, and jobs.”